Cisco Asa Crypto Key Generate Rsa Command
Posted By admin On 13.12.20- Generate A Rsa Crypto Key
- Cisco Crypto Key Generate Rsa
- Crypto Key Generate Rsa 1024
- Cisco Asa Crypto Key Generate Rsa Command Download
- Generate Rsa Key Command
- Cisco Asa Crypto Key Generate Rsa Commands
ASA-5505 (config)# domain-name networkjutsu.com ASA-5505 (config)# crypto key gen rsa mod 4096 ASA-5505 (config)# ssh version 2 ASA-5505 (config)# ssh key-exchange group dh-group14-sha1. As you know, it is a good idea to enable SSH and disable Telnet. Since ASA does not enable SSH and/or Telnet by default, you have less to worry about.
- Solved: I read from the manual that the key pair will be used for SSH but just wonder does the command 'crypto key generate rsa' is necessary to enable SSH on ASA? I can access to my firewall via SSH but when I checked in the configuration on ASA.
- Configuring Authentication of Administrative Sessions. To allow the Cisco ASA to use the local database as a fallback method. # domain-name cisco.com New York(config)# crypto key generate rsa modulus 2048 INFO: The name for the keys will be: ASA.cisco.com Keypair generation process begin.
Remote Management Access to ASA and FWSM
The examples presented so far have considered that there was physical access to the console port of the appliance (or to the hosting Catalyst 6500 for the FWSM). This section examines management connections that rely on remote access protocols (Telnet, SSH, and HTTPS).
Telnet Access
Telnet is a classic terminal access protocol that has received much criticism because of its clear text nature. It is highly recommended you replace it with SSH, which provides confidentiality.
At any rate, Telnet can still be useful for testing purposes mainly during initial setup. The commands shown in Example 3-15 specify the following:
Generate A Rsa Crypto Key
- Telnet access is accepted only when it is initiated from source addresses on network 192.168.1.0/24. Further, the packets must arrive through the logical interface called mgmt.
- The authentication of users who have permission to Telnet to the firewall is done using the LOCAL database. (LOCAL is a reserved keyword for ASA and FWSM.)
- The username admin is included in the LOCAL database.
Example 3-15 also displays a sample Telnet session coming from address 192.168.1.201.
Example 3-15. Configuring and Verifying Telnet Access
SSH Access
If remote CLI access to the firewalls is needed, SSH is the protocol of choice. It provides the same terminal services that Telnet does but with the significant advantage of encrypting traffic between client and server (the firewall receiving the connection).
Because SSH uses RSA public keys to encrypt the sessions, you need to have consistent timing information. Example 3-16 shows not only how to manually adjust and verify timing information, but also how to create a domain name and generate RSA keys.
Example 3-17 shows how to visualize SSH-related information in the Running-config. Notice that the default timeout value for SSH sessions is 5 minutes.
Example 3-16. Recommended Tasks Before Starting SSH Configuration
Example 3-17. SSH Configuration
HTTPS Access Using ASDM
The Adaptive Security Device Manager (ASDM) is an intuitive and easy-to-use GUI that accompanies every member of the ASA family. The interface provides a nice graphical abstraction for the actual commands that are used not only to implement the features but also to verify their operation, thus allowing users who are already familiar with classic firewall concepts (even from other vendors) to easily adapt their knowledge to the new GUI and immediately start working.
Documenting ASDM usage with its uncountable configuration and monitoring screens is beyond the scope of this book. However, the preparation of firewall devices to accommodate ASDM management is covered.
ASDM uses the HTTPS protocol for communications between the management station and the firewall. After properly loading the ASDM image on the device's flash memory, a web browser can be employed for the first access to the device, with the underlying goal of installing the ASDM launcher application on the administrator's PC.
Example 3-18 shows the preliminary tasks for enabling HTTPS access and assumes that the remote user has been granted the highest privilege level (priv-lvl = 15) and that the requests arrive though the logical interface called mgmt. In the example, the user named admin is authenticated against the LOCAL database and should start the management session from a host that belongs to the 192.168.1.0/24 subnet. The example also contains information about location of the ASDM image in the device flash (disk0: in this case) and how to find it within the show version output.
Example 3-18. Enabling HTTPS Access on ASA
Figure 3-4 portrays the web browser access to the HTPPS server on the device whose management interface is configured with the address 192.168.1.2 (https://192.168.1.2).
Figure 3-4 First HTTPS Access and Initial ASDM Page
From this screen, select the Install ASDM Launcher and Run ASDM option and follow these steps:
- Step 1. Authenticate with the credentials configured in Example 3-18 when the Connect to 192.168.1.2 window displays.
- Step 2. From the File Download - Security Warning window, save the '.msi' file locally.
- Step 3. Run the '.msi' file and install the ASDM Launcher application.
- Step 4. After starting the ASDM Launcher, fill in the IP address (192.168.1.2 in this case) and the credentials (username/password).
- Step 5. After accepting the device certificate, the main ASDM page displays (Figure 3-5). This screen summarizes information for the device, including available licenses, interface status, and system resources status.
Figure 3-6 depicts the base ASDM screen for Interface Configuration on an ASA 5505 appliance. Notice that the full path to this particular screen, Configuration > Device Setup> Interfaces, displays on the top of the right pane.
Figure 3-6 Base ASDM Page for Interface Configuration
Figure 3-7 shows a sample ASDM screen that helps perform the Monitoring task of verifying the ARP table. The complete path for viewing this table is represented at the top of the right pane (Monitoring > Interfaces > ARP Table).
Figure 3-7 Base ASDM Page for ARP Table Monitoring
Q: I have a Cisco switch in my network, which I can access by hooking up a console cable directly to the device. I like to access the switch remotely using SSH. How can I enable ssh on my Cisco 3750 Catalyst Switch?
A: By default, when you configure a Cisco device, you have to use the console cable and connect directly to the system to access it. Follow the steps mentioned below, which will enable SSH access to your Cisco devices. Once you enable SSH, you can access it remotely using PuTTY or any other SSH client.
1. Setup Management IP
First, make sure you have performed basic network configurations on your switch. For example, assign default gateway, assign management ip-address, etc. If this is already done, skip to the next step.
In the following example, the management ip address is set as 192.168.101.2 in the 101 VLAN. The default gateway points to the firewall, which is 192.168.101.1
2. Set hostname and domain-name
Next, make sure the switch has a hostname and domain-name set properly.
3. Generate the RSA Keys
The switch or router should have RSA keys that it will use during the SSH process. So, generate these using crypto command as shown below.
Also, if you are running on an older Cisco IOS image, it is highly recommended that you upgrade to latest Cisco IOS.
4. Setup the Line VTY configurations
Setup the following line vty configuration parameters, where input transport is set to SSH. Set the login to local, and password to 7.
If you have not set the console line yet, set it to the following values.
5. Create the username password
Cisco Crypto Key Generate Rsa
If you don’t have an username created already, do it as shown below.

Note: If you don’t have the enable password setup properly, do it now.
Make sure the password-encryption service is turned-on, which will encrypt the password, and when you do “sh run”, you’ll seee only the encrypted password and not clear-text password.
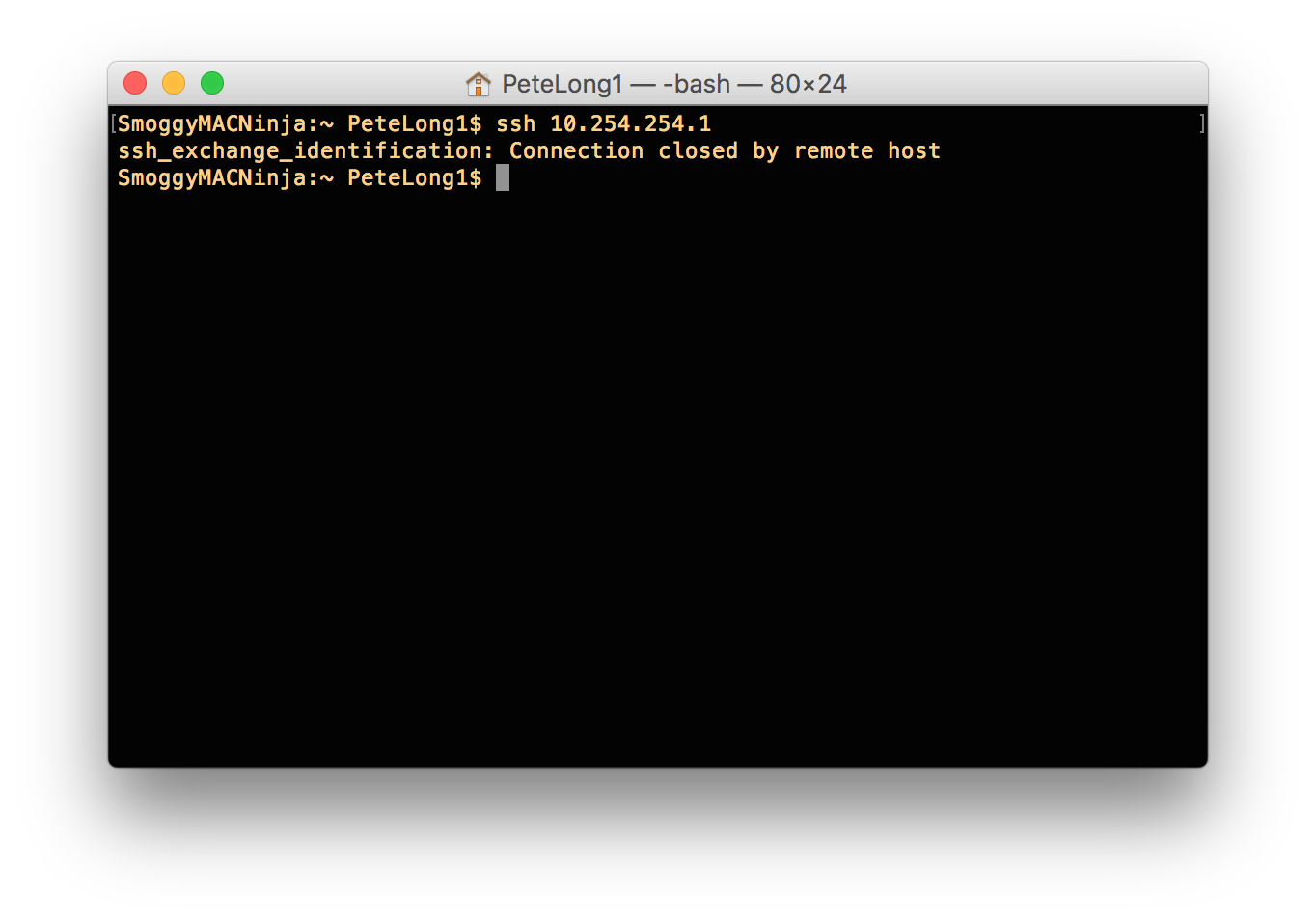
5. Verify SSH access
From the switch, if you do ‘sh ip ssh’, it will confirm that the SSH is enabled on this cisco device.
Crypto Key Generate Rsa 1024
After the above configurations, login from a remote machine to verify that you can ssh to this cisco switch.
In this example, 192.168.101.2 is the management ip-address of the switch.
Cisco Asa Crypto Key Generate Rsa Command Download
If you enjoyed this article, you might also like..
Generate Rsa Key Command
Cisco Asa Crypto Key Generate Rsa Commands
Next post: How to Backup Oracle Database using RMAN (with Examples)
Previous post: How to Use C++ Single and Multiple Inheritance with an Example